In today’s world, we rely heavily on digital transactions for everything from purchasing groceries to booking flights. While the convenience of e-commerce has transformed how we shop and manage our finances, it has also opened the door to new and sophisticated types of cybercrime. One such threat involves illegal online platforms, often referred to as “Ultimate Shops,” where stolen financial data such as credit card details, known as “dumps” and “CVV2,” are bought and sold. In this article, we will explore what the “Ultimate Shop” is, the role of dumps and CVV2 in online fraud, and how these illegal activities affect our security. We’ll also discuss how individuals can protect themselves from becoming victims of such crimes.
What Is the “Ultimate Shop”?
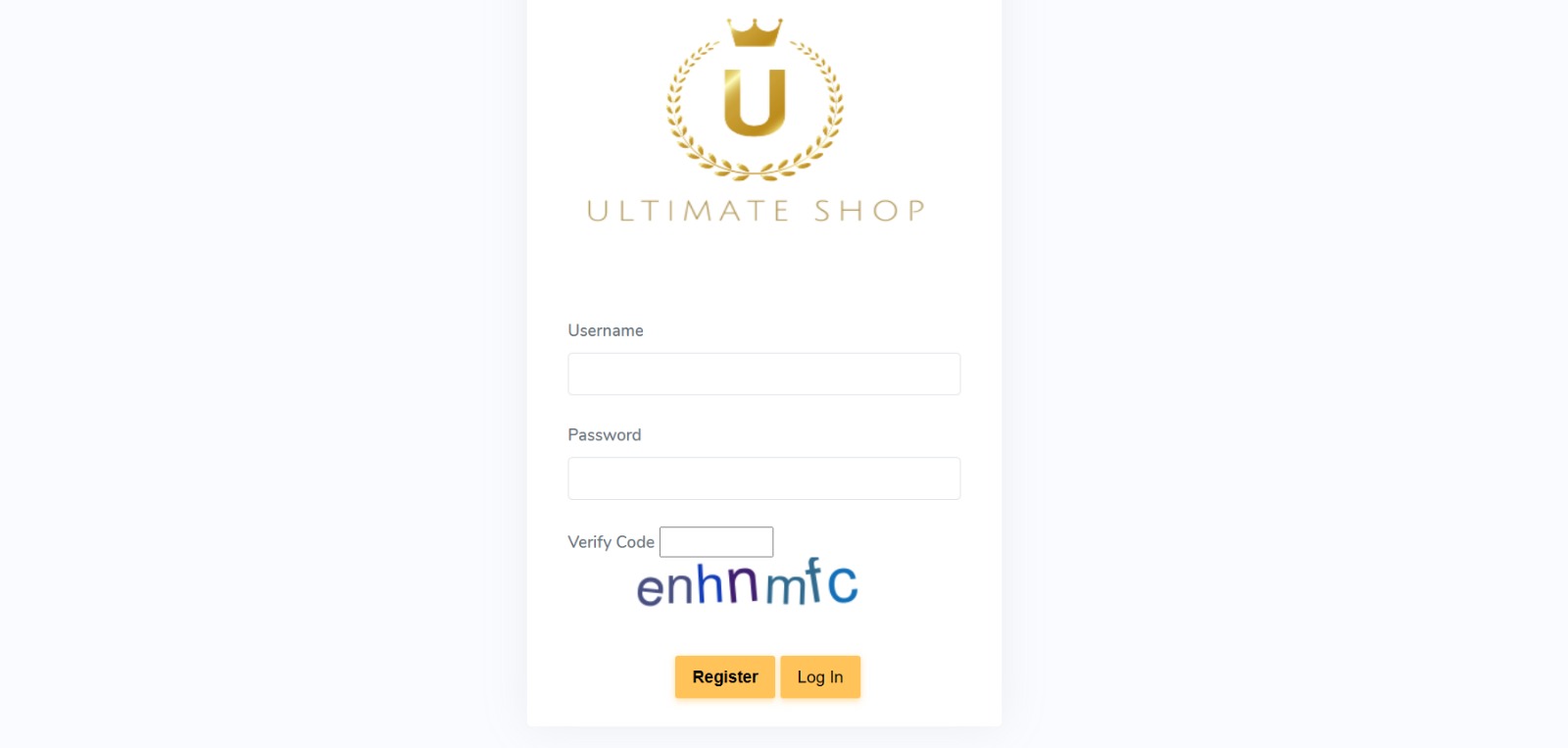
The term “Ultimate Shop” might sound like a regular online store, but it refers to illicit marketplaces on the dark web where stolen financial information is traded. These platforms do not sell traditional consumer goods like electronics or clothing. Instead, they specialize in selling stolen credit card data, banking details, and other forms of personal information. These marketplaces are typically hidden on the dark web, which requires special software, such as Tor, to access.
The “Ultimate Shop” exists in the shadows of the internet, catering to criminals who seek stolen financial data for various illegal activities. By purchasing this information, fraudsters can engage in unauthorized transactions, create counterfeit cards, or commit other financial crimes. Because these shops operate out of reach of law enforcement, they are difficult to shut down and can cause widespread harm to consumers and businesses alike.
These sites might appear to be legitimate e-commerce platforms at first glance, but their focus is on enabling fraud. If you’re unaware of their existence, it can be easy to assume that the digital world is safe. However, understanding how these dark-web marketplaces operate is key to safeguarding your personal information from such threats.
What Are Dumps?
In the context of card fraud, the term “dump” refers to the stolen data extracted from a credit card’s magnetic stripe. Every time a person swipes their credit card at a payment terminal, the device reads the magnetic stripe, which contains important information about the cardholder. This data includes the card number, expiration date, and other details such as the cardholder’s name.
Dumps are stolen using a technique called “skimming,” where fraudsters install small, hidden devices (called skimmers) on ATMs or point-of-sale terminals. These devices capture the data from the card’s magnetic stripe when an individual inserts their card into the machine. Criminals who successfully steal this data can then use it to clone the card or make unauthorized transactions.
Once they have collected this data, criminals can sell it on illegal platforms like the “Ultimate Shop,” where buyers can purchase the stolen dumps and use them for their own fraudulent activities. This data is highly valuable because it contains everything necessary to access a victim’s account or make purchases using their card. In many cases, fraudsters combine the stolen dump with other details (such as CVV2 codes) to increase the chances of successfully completing a transaction.
What Is CVV2 and Why Is It Important?
CVV2 stands for “Card Verification Value 2,” which is a three-digit security code printed on the back of most credit and debit cards. This code is used to confirm that the person making a transaction is physically in possession of the card, adding an extra layer of security when making purchases online or over the phone. For example, when you shop online, you’re often asked to provide the card number, expiration date, and CVV2 to verify your identity.
In fraud, CVV2 codes are especially important. A criminal who steals a credit card number can make online purchases with it, but if they don’t have the CVV2, they might be blocked by merchants’ fraud protection systems. However, when criminals obtain both the dump (the stolen card data) and the CVV2 code, they have everything needed to complete an online purchase, making it much harder for merchants to detect fraud.
This is why CVV2 codes are a highly sought-after commodity in the dark web marketplaces, such as the “Ultimate Shop.” Fraudsters who have access to both the card number and CVV2 code can easily bypass security checks and make fraudulent purchases with a stolen card. It’s an essential piece of the puzzle when it comes to executing card fraud.
How Are Dumps and CVV2 Used in Fraud?
The combination of dumps and CVV2 codes creates the perfect opportunity for criminals to commit a wide range of fraud. Once fraudsters obtain both pieces of information, they can exploit them in several ways:
-
Counterfeit Card Creation: One of the most common methods fraudsters use is creating counterfeit cards. With a stolen dump and the associated CVV2 code, criminals can encode the stolen data onto a blank card. This allows them to produce a fully functional counterfeit credit card that can be used for in-person purchases or ATM withdrawals. The CVV2 code is crucial in making the card appear legitimate, especially for online transactions where merchants require the code for verification.
-
Online Purchases: The combination of stolen dumps and CVV2 codes allows criminals to make online purchases without the physical card. Most online merchants ask for the CVV2 during checkout to prevent fraud, but when fraudsters have this code, they can complete transactions undetected. This means that even if the cardholder never uses the card, criminals can still make unauthorized purchases, sometimes without triggering any alerts.
-
Reselling Stolen Data: Not all criminals who steal card information use it themselves. Some prefer to sell it on illegal marketplaces, like the “Ultimate Shop.” Once the data is stolen, it can be resold multiple times, allowing other criminals to exploit the information for their own purposes. This perpetuates a cycle of fraud and makes it harder for law enforcement to trace and catch the criminals responsible.
-
Money Laundering: After committing fraud, criminals may engage in money laundering to hide the origin of the stolen funds. One way they do this is by purchasing goods using stolen card information, which they can later resell for cash. This allows them to disguise the source of the funds and make it more difficult for authorities to trace the stolen money.
The Risks of Engaging with an “Ultimate Shop”
Participating in an “Ultimate Shop” or similar illegal marketplace is not only unethical, but it’s also illegal. Buying or selling stolen data, such as dumps and CVV2 codes, can lead to severe legal consequences. Criminals who are caught engaging in these activities can face hefty fines, prison sentences, and a lifetime of legal issues.
Additionally, the harm caused by these fraud schemes extends beyond the criminals themselves. The victims of card fraud often experience financial losses, damaged credit, and months, if not years, of efforts to regain control over their financial accounts. Identity theft is a common consequence of financial fraud, and it can take a significant toll on the victim’s life. Recovering from such an experience can be exhausting and costly.
Moreover, the broader impact of online fraud is felt by businesses, particularly financial institutions and e-commerce platforms. These companies incur significant costs when fraud occurs, leading to higher prices for consumers and a decline in trust in online transactions. The continued existence of platforms like the “Ultimate Shop” contributes to the ongoing problem of cybercrime, making it more difficult for legitimate businesses to thrive.
How Can You Protect Yourself from Card Fraud?
Given the prevalence of online fraud, it’s essential to take steps to protect your personal and financial information. Here are a few simple yet effective ways to reduce the risk of becoming a victim:
-
Use Secure Payment Methods: Opt for payment services like PayPal or digital wallets, which don’t require you to input your card details directly with merchants. These services offer an added layer of protection against fraud.
-
Monitor Your Financial Accounts: Regularly check your bank and credit card statements for any unauthorized transactions. Early detection can help minimize the damage caused by fraud.
-
Enable Two-Factor Authentication: Many financial institutions and online services offer two-factor authentication (2FA), which provides an extra layer of security. Enable this feature whenever possible to prevent unauthorized access to your accounts.
-
Use Strong Passwords: Ensure your online accounts are protected with strong, unique passwords. Avoid using the same password for multiple accounts, as this makes it easier for fraudsters to gain access to your information.
-
Be Cautious with Your Data: Only provide your personal and financial information on trusted websites with secure connections. Look for HTTPS in the URL and avoid clicking on suspicious links in emails or text messages.
Conclusion
The “Ultimate Shop” and similar dark-web marketplaces represent a significant threat to online security. By selling stolen card data, including dumps and CVV2 codes, they enable criminals to carry out fraudulent activities with ease. However, by staying informed and taking proactive measures to protect your personal information, you can reduce your risk of becoming a victim. It’s essential to adopt safe practices for online transactions, monitor your financial accounts, and stay vigilant against potential threats. Together, we can help create a safer digital world and protect ourselves from the dangers of online fraud.